Zero trust is a security principle which emphasizes that security networks should “always verify, never trust” any device, including those already within the network perimeter. As a result, a zero trust security framework demands that any device accessing network resources provide authentication through micro-segmented security checkpoints to minimize user error and provide a more secure network interaction.
- Secure your deployments with device geofencing & GPS tracking
- Get strong integrity using hardware & software encryption via TPM
- Protect users & data with multi-factor authentication & fine-grain authorization
Why choose zero trust?
Traditional “castle and moat” security models don’t address either the user error involved in modern cyberattacks or the expansion of the network perimeter due to the rise of remote work. Instead, a zero trust security framework focuses on the devices themselves and disregards the perimeter as the primary judge of a device’s trustworthiness.
- Protect your entire enterprise, including remote workers
- Get core-to-edge data protection & stay safe from attacks
- Set up new networks with hardened security, even before Day 0
The use of zero trust in remote networks also frees up the back and forth traffic that normally has to be routed through your already overworked data center. This lightens the load on network engineers and creates a more user-friendly experience for your staff.
The ultimate zero trust learning center
Want to know what zero trust offers your large enterprise?
Not sure about the fundamentals of zero trust?
Want information about the future of zero trust?
Are you struggling with the concept of Micro-segmentation?
How can an enterprise implement a zero trust architecture?
What does zero trust look like in an enterprise setting?
How does zero trust work with edge architectures like Secure Access Service Edge (SASE)?
Security that scales with you
The latest in geofencing & GPS technology allows you to customize your security configuration. Nodegrid’s secure boot verifies the OS software signature before running so you get a solid zero trust security framework that protects you, even at scale.
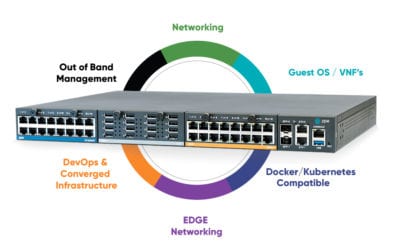
Nodegrid’s hardware and software features allow you to customize your zero trust security framework. These built-in integrations include:
Secure boot, custom security profile & port authentication
Password-protected BIOS/Grub and signed software
Latest kernel & cryptographic modules
64-bit OS with current encryption and security patches
SSO with SAML (Duo, Okta, Ping and ADFS), 2FA, & remote authentication
Remote access to cloud & devices with enterprise grade authentication
Geofence perimeter crossing detection and security prevention
Tracks IT device’s GPS coordinates
Take customizable actions and protect your information
Strong password enforcement
Password configuration and expiration
Fine grain authorization & RBAC
Control access, targets, & actions
Firewall, IPSec, & Fail2Ban intrusion prevention
Native protection and 3rd-party extensibility
Tampering protection & configuration reset
Configuration checksum and changes detection
Configuration ‘reset’ button easily reconnects to ZPE Cloud
Hardware encrypted storage using TPM
No performance impact due to software encryption
Cloud management, control, & access
Consistent configuration across branches
802.1x network port authentication
No unauthorized network access
360° monitoring, with logging, alerts, & actions
Trail logs, compliance- and protection-ready
Selectable protocols & cyphers
Allow only what you need
Lock what is not required
Zero trust security framework is about partnerships
Zero trust relies on your security stack working together. Luckily, Nodegrid was made to integrate.
Tested and verified to work with leading SAML providers, Nodegrid zero trust security framework works with you to create a platform that integrates with SSE vendors of your choice. Customize your security by integrating with companies like Duo, Okta, Ping Identity, Microsoft ADFS, and others.




Never trust, always verify
A Zero Trust Security Framework pulls from a robust toolbox of features designed to provide you with the latest in around-the-clock security.

Segmentation
Create micro segments to designate your network perimeters and strengthen your security layer.

Multi-factor authentication
Require multi-factor authentication (MFA) that ensures only the right users & devices gain access.

Least-privilege access
Let users access the network resources they need, without exposing them to areas outside their competency or duty.
Learn more about Zero Trust Security
Cisco ISR 4431 EOL Replacement Guide
The Cisco ISR 4431 is an enterprise branch services router from Cisco’s Integrated Services Router product line. The ISR 4431 integrates with the Cisco DNA infrastructure management platform and the...
Cisco 4351 EOL Replacement Guide
The Cisco 4351 comes from the Integrated Services Router (ISR) product line of enterprise branch WAN solutions. The ISR 4351 works with Cisco’s software-defined wide area networking (SD-WAN)...
The Future of Edge Computing
Edge computing moves computing resources and data processing applications out of the centralized data center or cloud, deploying them at the edges of the network and allowing companies to use their...
Streamline your security stack with zero trust security framework
ZPE Systems’ zero trust security framework offers a flexible, comprehensive platform to implement and regulate zero trust to meet all your enterprise’s security needs.
Want to learn more? Contact us or book a free demo to discover how Nodegrid can help you establish zero trust, build a SASE network, and keep all your users secure